
性能VS安全?CPU芯片漏洞攻击实战(2) – Meltdown获取Linux内核数据
https://weibo.com/ttarticle/p/show?id=2309404192925885035405
Intel CPU漏洞简述
https://weibo.com/ttarticle/p/show?id=2309404192902644407039
Arm写的关于Arm对此次CPU漏洞涉及的技术的细节,并给出了Arm平台对漏洞的缓解措施
https://armkeil.blob.core.windows.net/developer/Files/pdf/Cache_Speculation_Side-channels.pdf
检测是否受此次CPU漏洞影响的工具(目前仅Linux平台)
https://github.com/raphaelsc/Am-I-affected-by-Meltdown
微软发布防御此次的Spectre/Meltdown漏洞的指南(含PowerShell脚本)
为什么树莓派不受SPECTRE/MELTDOWN漏洞影响?
https://www.raspberrypi.org/blog/why-raspberry-pi-isnt-vulnerable-to-spectre-or-meltdown/
Cisco IOS SNMP 远程代码执行漏洞CVE-2017-6737 exploit
https://github.com/artkond/cisco-snmp-rce
Google Play发现22多款手电筒app中发现恶意代码,已达百万下载量
ReverseCrypt:提取加密Jar包的工具
https://github.com/GraxCode/ReverseCrypt
移动安全人员逆向了朝鲜的”数字签名处理系统” Android app
https://github.com/fs0c131y/RedFlag
Striker:信息搜集/漏洞扫描工具
https://github.com/UltimateHackers/Striker
VMware Workstation – ALSA配置文件本地提权
https://www.exploit-db.com/exploits/43449/
Reposcanner:扫描git项目字符串的工具
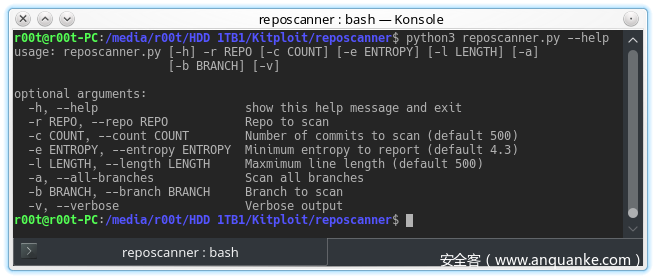
https://www.kitploit.com/2018/01/reposcanner-python-script-to-scan-git.html
安全客小编2
如若转载,请注明出处: https://www.anquanke.com/post/id/93824